#ShowYourStripes now!
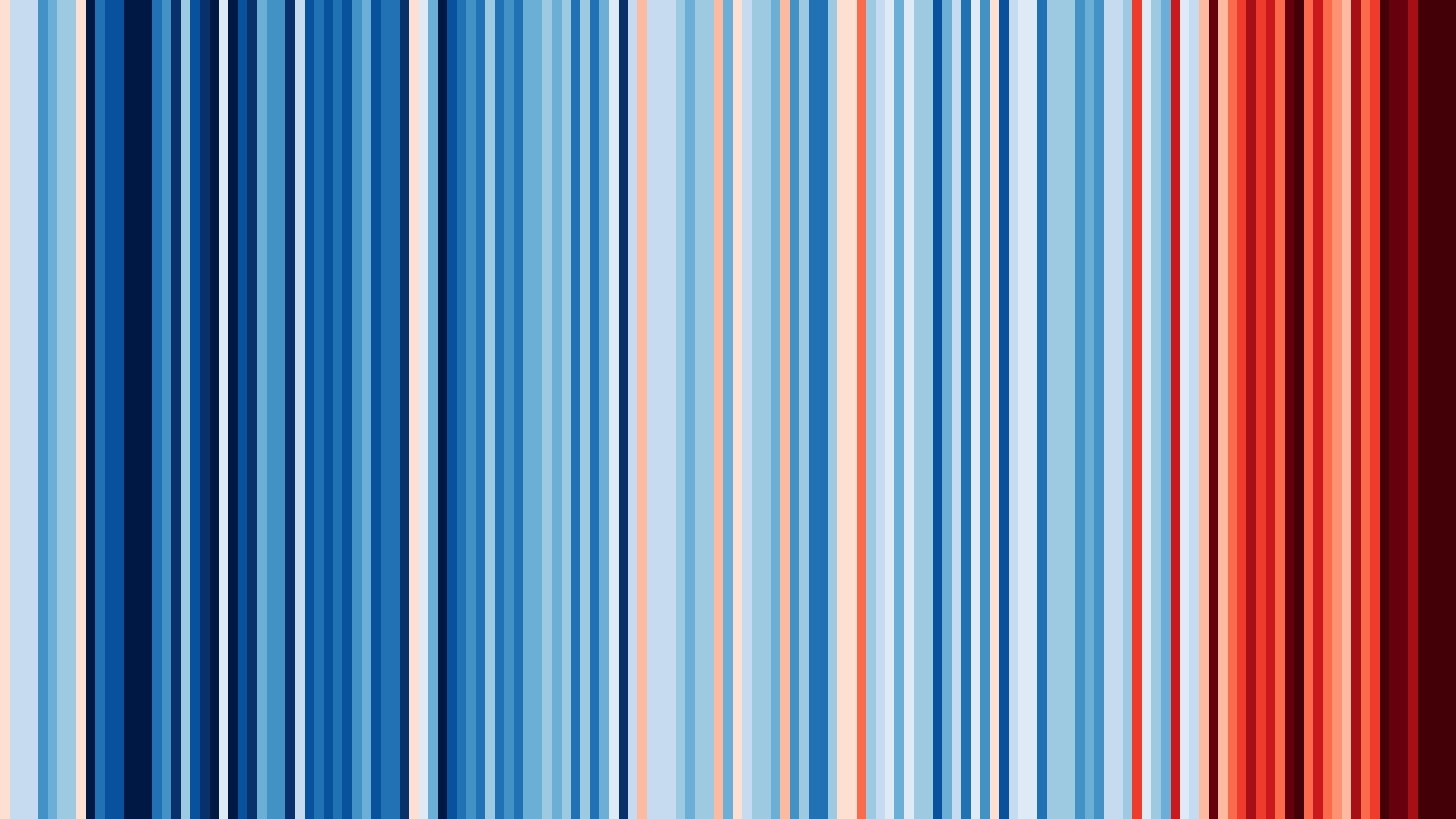
#ShowYourStripes illustrates the climate change for your region from 1850 to today!
This is for Shanghai!
Checkout the specific temperature changes by visiting showyourstripes.info
Chinesisches Neujahrsfest 2024: Willkommen im Jahr des Drachens

Seite heute, dem 10. Februar 2024, befinden wir uns laut dem Chinesischen Mondkalender im Jahr des Drachens.
新年快乐! (Pinyin: Xīnnián kuàilè – gesprochen etwa “chin niän kwei le”) – HAPPY NEW YEAR – EIN FROHES NEUES JAHR!
Ich wünsche Euch allen und Euren Familien, Freunden und Lieben alles Gute und einen glückliches und segensreiches Jahr des Drachen!
Hier die Kombination der 12 Tierkreiszeichen und der Elemente für die Jahre 1864 bis 2103
Welches chinesische Tierkreiszeichen hast Du?
| Element | Tier | Symbol | Jahre | |||
|---|---|---|---|---|---|---|
| Holz | Ratte | 甲子 | 1864 | 1924 | 1984 | 2044 |
| Holz | Büffel | 乙丑 | 1865 | 1925 | 1985 | 2045 |
| Feuer | Tiger | 丙寅 | 1866 | 1926 | 1986 | 2046 |
| Feuer | Hase | 丁卯 | 1867 | 1927 | 1987 | 2047 |
| Erde | Drache | 戊辰 | 1868 | 1928 | 1988 | 2048 |
| Erde | Schlange | 己巳 | 1869 | 1929 | 1989 | 2049 |
| Metall | Pferd | 庚午 | 1870 | 1930 | 1990 | 2050 |
| Metall | Schaf | 辛未 | 1871 | 1931 | 1991 | 2051 |
| Wasser | Affe | 壬申 | 1872 | 1932 | 1992 | 2052 |
| Wasser | Hahn | 癸酉 | 1873 | 1933 | 1993 | 2053 |
| Holz | Hund | 甲戌 | 1874 | 1934 | 1994 | 2054 |
| Holz | Schwein | 乙亥 | 1875 | 1935 | 1995 | 2055 |
| Feuer | Ratte | 丙子 | 1876 | 1936 | 1996 | 2056 |
| Feuer | Büffel | 丁丑 | 1877 | 1937 | 1997 | 2057 |
| Erde | Tiger | 戊寅 | 1878 | 1938 | 1998 | 2058 |
| Erde | Hase | 己卯 | 1879 | 1939 | 1999 | 2059 |
| Metall | Drache | 庚辰 | 1880 | 1940 | 2000 | 2060 |
| Metall | Schlange | 辛巳 | 1881 | 1941 | 2001 | 2061 |
| Wasser | Pferd | 壬午 | 1882 | 1942 | 2002 | 2062 |
| Wasser | Schaf | 癸未 | 1883 | 1943 | 2003 | 2063 |
| Holz | Affe | 甲申 | 1884 | 1944 | 2004 | 2064 |
| Holz | Hahn | 乙酉 | 1885 | 1945 | 2005 | 2065 |
| Feuer | Hund | 丙戌 | 1886 | 1946 | 2006 | 2066 |
| Feuer | Schwein | 丁亥 | 1887 | 1947 | 2007 | 2067 |
| Erde | Ratte | 戊子 | 1888 | 1948 | 2008 | 2068 |
| Erde | Büffel | 己丑 | 1889 | 1949 | 2009 | 2069 |
| Metall | Tiger | 庚寅 | 1890 | 1950 | 2010 | 2070 |
| Metall | Hase | 辛卯 | 1891 | 1951 | 2011 | 2071 |
| Wasser | Drache | 壬辰 | 1892 | 1952 | 2012 | 2072 |
| Wasser | Schlange | 癸巳 | 1893 | 1953 | 2013 | 2073 |
| Holz | Pferd | 甲午 | 1894 | 1954 | 2014 | 2074 |
| Holz | Schaf | 乙未 | 1895 | 1955 | 2015 | 2075 |
| Feuer | Affe | 丙申 | 1896 | 1956 | 2016 | 2076 |
| Feuer | Hahn | 丁酉 | 1897 | 1957 | 2017 | 2077 |
| Erde | Hund | 戊戌 | 1898 | 1958 | 2018 | 2078 |
| Erde | Schwein | 己亥 | 1899 | 1959 | 2019 | 2079 |
| Metall | Ratte | 庚子 | 1900 | 1960 | 2020 | 2080 |
| Metall | Büffel | 辛丑 | 1901 | 1961 | 2021 | 2081 |
| Wasser | Tiger | 壬寅 | 1902 | 1962 | 2022 | 2082 |
| Wasser | Hase | 癸卯 | 1903 | 1963 | 2023 | 2083 |
| Holz | Drache | 甲辰 | 1904 | 1964 | 2024 | 2084 |
| Holz | Schlange | 乙巳 | 1905 | 1965 | 2025 | 2085 |
| Feuer | Pferd | 丙午 | 1906 | 1966 | 2026 | 2086 |
| Feuer | Schaf | 丁未 | 1907 | 1967 | 2027 | 2087 |
| Erde | Affe | 戊申 | 1908 | 1968 | 2028 | 2088 |
| Erde | Hahn | 己酉 | 1909 | 1969 | 2029 | 2089 |
| Metall | Hund | 庚戌 | 1910 | 1970 | 2030 | 2090 |
| Metall | Schwein | 辛亥 | 1911 | 1971 | 2031 | 2091 |
| Wasser | Ratte | 壬子 | 1912 | 1972 | 2032 | 2092 |
| Wasser | Büffel | 癸丑 | 1913 | 1973 | 2033 | 2093 |
| Holz | Tiger | 甲寅 | 1914 | 1974 | 2034 | 2094 |
| Holz | Hase | 乙卯 | 1915 | 1975 | 2035 | 2095 |
| Feuer | Drache | 丙辰 | 1916 | 1976 | 2036 | 2096 |
| Feuer | Schlange | 丁巳 | 1917 | 1977 | 2037 | 2097 |
| Erde | Pferd | 戊午 | 1918 | 1978 | 2038 | 2098 |
| Erde | Schaf | 己未 | 1919 | 1979 | 2039 | 2099 |
| Metall | Affe | 庚申 | 1920 | 1980 | 2040 | 2100 |
| Metall | Hahn | 辛酉 | 1921 | 1981 | 2041 | 2101 |
| Wasser | Hund | 壬戌 | 1922 | 1982 | 2042 | 2102 |
| Wasser | Schwein | 癸亥 | 1923 | 1983 | 2043 | 2103 |
Being named as a new contributor in the latest release of #btcd v0.24.0
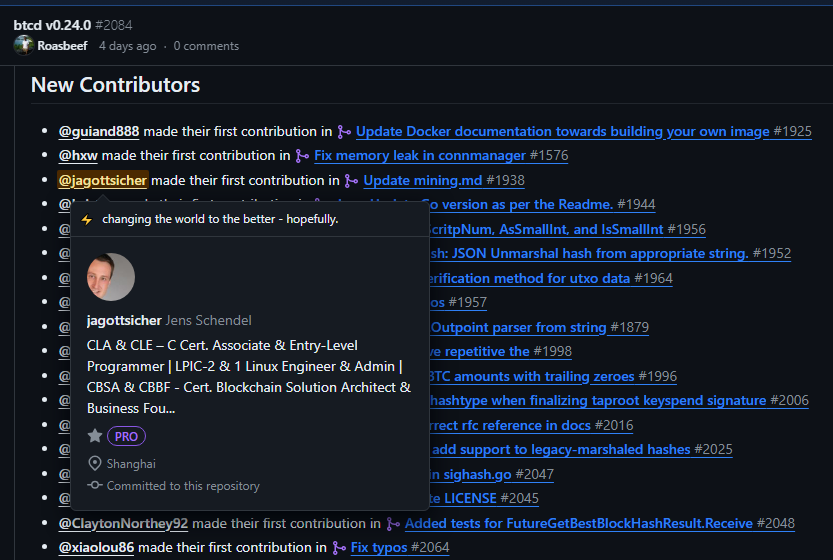
Being named as a new contributor in the latest release of #btcd v0.24.0 is too much of an honor. I just made a suggestion in http://mining.md on how to copy something easier. But nice to see that there is a new #Bitcoin client available!
Papa hat gekocht

Papa hat gekocht: Grünkohleintopf! #yummy
Papa hat gekocht

Papa hat gekocht: Armer Ritter ist ein Essen für dass man weder arm noch Ritter sein muss 🤷♂️
Chinesische Feiertage 2024
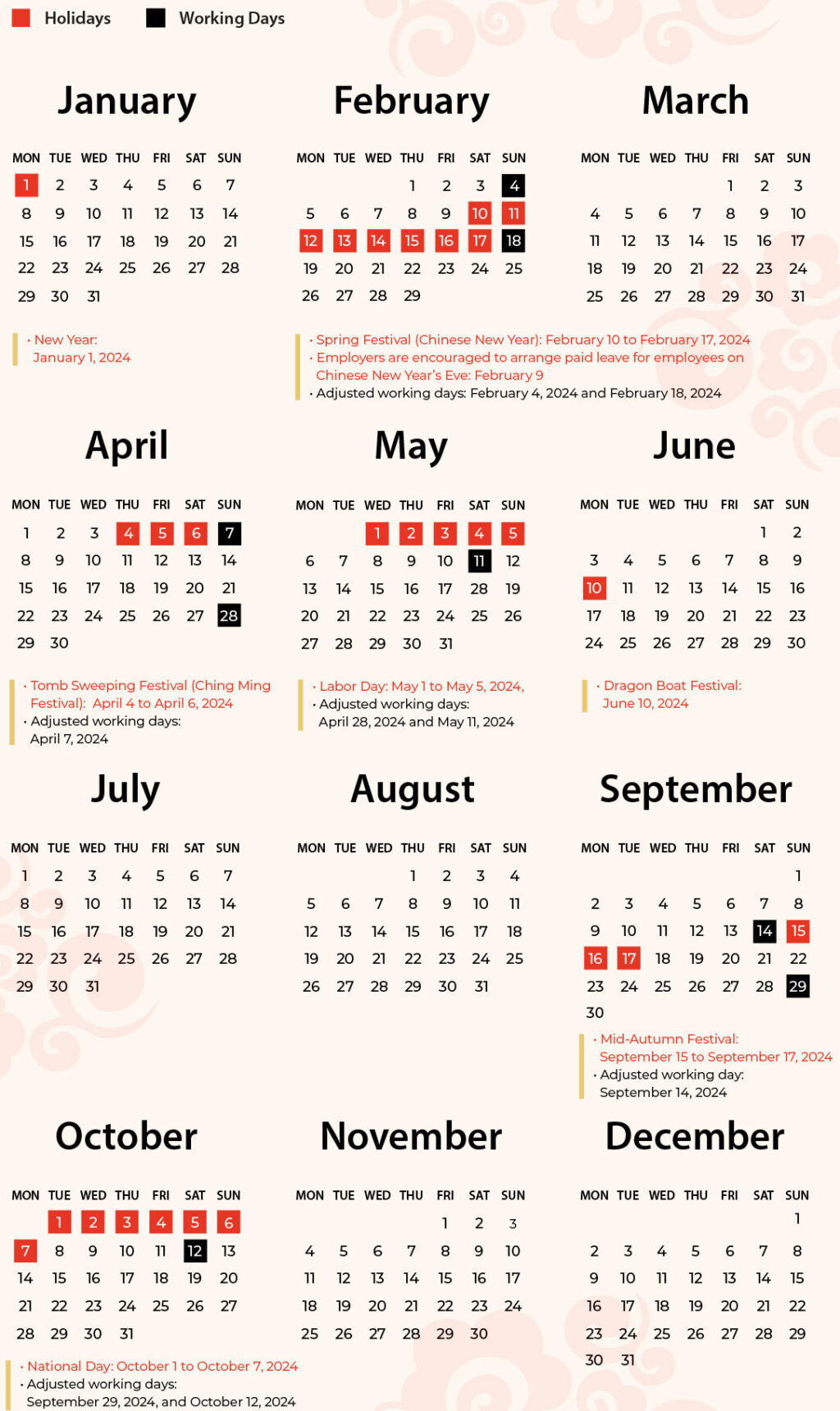
Official China Public Holiday 2024 schedule
New Year
- January 1, 2024 (one rest day)
Spring Festival (Chinese New Year)
- February 10 to February 17, 2024 (eight rest days in total)
- Employers are encouraged to arrange paid leave for employees on Chinese New Year’s Eve (February 9)
- Adjusted working days: February 4, 2024 (Sunday) and February 18, 2024 (Sunday)
Tomb Sweeping Festival (Ching Ming Festival)
- April 4 to April 6, 2024 (three rest days in total, in connection with one weekend day)
- Adjusted working days: April 7, 2024 (Sunday)
Labor Day
- May 1 to May 5, 2024 (five rest days in total)
- Adjusted working days: April 28, 2024 (Sunday) and May 11, 2024 (Saturday)
Dragon Boat Festival
- June 10, 2024 (three rest days in total, in connection with the weekend)
Mid-Autumn Festival
- September 15 to September 17, 2024 (three rest days in total)
- Adjusted working days: September 14, 2024 (Saturday)
National Day
- October 1 to October 7, 2024 (seven rest days in total)
- Adjusted working days: September 29, 2024 (Sunday) and October 12, 2024 (Saturday)
Bisq: Empowering You in the World of Cryptocurrency Trading

In the ever-evolving realm of cryptocurrency trading, security, privacy, and transparency have become paramount. Bisq, the decentralized exchange platform hosted at bisq.network, stands as a beacon of innovation, offering users a truly peer-to-peer experience in the world of digital currencies.
How Bisq Works
At its core, Bisq operates as a decentralized exchange network, allowing users to buy and sell cryptocurrencies directly with one another. Unlike traditional exchanges, Bisq cuts out the middleman, empowering users with direct control over their transactions. This open-source platform facilitates secure trades, ensuring that your funds and personal data remain in your hands.
Advantages of Decentralization
Decentralization, the cornerstone of Bisq, offers a myriad of advantages over centralized platforms. First and foremost, decentralization eliminates the need for intermediaries, reducing the risk of hacks and ensuring that you retain ownership of your assets throughout the trading process. Additionally, decentralized exchanges are not bound by geographical restrictions, providing a truly global marketplace for cryptocurrency enthusiasts.
Bisq’s Focus on Privacy
Privacy is not just a feature at Bisq; it’s a fundamental right. Bisq employs innovative techniques like Tor and end-to-end encryption to protect your identity and transaction data. With Bisq, you can trade confidently, knowing that your personal information is shielded from prying eyes. The platform never holds your funds, further enhancing the security of your assets. Never forget: Not your keys, not your Bitcoin!
In a world where data breaches and privacy concerns abound, Bisq stands as a testament to the power of decentralized, peer-to-peer trading. By leveraging cutting-edge technology and a commitment to user empowerment, Bisq provides a safe, private, and transparent environment for cryptocurrency enthusiasts.
Embrace the future of trading with Bisq – where your security, privacy, and control are never compromised. Join the decentralized revolution and experience cryptocurrency trading like never before.
Take charge. Trade freely. Trust Bisq.
GO (golang): Develop Modern, Fast & Secure Web Applications
Over the past few months I have been working hard to develop a new course:
GO (golang): Develop Modern, Fast & Secure Web Applications – English
Now it’s practically finished and ready for the world!
During this challenging time, I’ve incorporated experiences from my previous courses and created the course with passion and care. But I know that there is always room for improvement. That is why I am reaching out to you to ask for your help.
I consider this course to be in a “beta testing” phase of sorts. Until October 15, 2023 4:11 PM PDT, I invite you to book the course for free on Udemy using coupon code MYGOWEBAPP-1000.
Your constructive critiques are invaluable. If you discover areas where I can improve the course, I am happy to make adjustments and/or add new lessons.
Your opinion is important not only to me, but also to other learners on Udemy. That’s why I also ask you to give me an honest rating and a few words as feedback. Your help will not only enrich the course but also the whole learning community.
Thank you in advance for your support. I am eager to hear your feedback and look forward to working with you to make this course even better.
GO (golang): Schnelle & sichere Webanwendungen programmieren

In den vergangenen Monaten habe ich hart daran gearbeitet, einen neuen Kurs zu entwickeln:
Go (Golang): Schnelle und sichere Webanwendungen programmieren
Jetzt ist er fast fertig und bereit für die Welt!
Während dieser Reise habe ich aus meinen früheren Kursen viel gelernt und diesen Kurs mit Leidenschaft und Sorgfalt erstellt. Doch ich weiß, dass es immer Raum für Verbesserungen gibt. Deshalb wende ich mich an Sie, um Ihre Hilfe zu bitten.
Ich sehe diesen Kurs als eine Art Beta-Testphase an. Bis zum 12. Oktober 2023 lade ich Sie herzlich ein, den Kurs kostenlos mit dem Gutscheincode MYGOWEBAPP auf Udemy zu buchen. Ihre konstruktive Kritik ist von unschätzbarem Wert. Wenn Sie Bereiche entdecken, in denen ich den Kurs verbessern kann, bin ich mehr als bereit, Anpassungen vorzunehmen und/oder neue Lektionen hinzuzufügen.
Ihre Meinung ist nicht nur für mich wichtig, sondern auch für andere Lernende auf Udemy. Deshalb bitte ich Sie auch um eine ehrliche Bewertung und einige Worte als Feedback. Ihre Hilfe wird nicht nur den Kurs, sondern auch die gesamte Lerngemeinschaft bereichern.
Vielen Dank im Voraus für Ihre Unterstützung. Ich bin gespannt auf Ihr Feedback und freue mich darauf, gemeinsam mit Ihnen diesen Kurs noch besser zu machen.
Money, wealth, fortune – how much is enough?


To #Bitcoin investors and enthusiasts panting after the “Lambo”, I recommend reading Andreas Eschenbach’s “One Trillion Dollars”.
$1,000,000,000,000 – a thousand billion!
What would you do with a trillion US Dollars?
Written in pre-Bitcoin era, it takes a sideways look at fiat money, corporations, global economy, mututal dependencies, predation, globalization, banks, governments, and reveals indirect connections that are rarely clear in the first – even after a longer look.
Can wealth pursue an ideology? For the good of all? Do interests make sense? Does wealth equal power? Does responsibility result from it?
Where would it begin and where would the limits of that responsibility be?
#Bitcoin fixes this.
or
#Bitcoin can fix this. 🤔


Den #Bitcoin Investoren und Enthusiasten, die dem „Lambo“ hinterher hecheln, empfehle ich Andreas Eschenbachs “Ein Billion Dollar” zu lesen.
1.000.000.000.000 $ – Tausend Milliarden!
Was würdest Du mit einer Billion US Dollar tun?
Geschrieben in der Prä-Bitcoin-Ära wirft es einen Seitenblick auf Fiatgeld, Konzerne, Abhängigkeiten, Raubbau, Globalisierung, Banken, Regierungen und enthüllt indirekte Zusammenhänge, die im Alltag selten — auch nach einem längeren Blick — klar sind.
Kann Reichtum eine Ideologie verfolgen? Zum Wohl aller? Machen Zinsen Sinn? Ist Reichtum gleich Macht? Resultiert daraus Verantwortung?
Wo begönne sie und wo wären Grenzen dieser Verantwortung?
#Bitcoin fixes this.
or
#Bitcoin can fix this. 🤔
I operate my own little Lightning Node
Feel free to open a channel e.g. with
clightning
lightning-cli connect 0366217f4a7abf70842f794e94a4cbddc249d5cbaf9c0ffd0b7e4638d9bf07845d 81.7.17.202 9735
lnd
lncli connect 0366217f4a7abf70842f794e94a4cbddc249d5cbaf9c0ffd0b7e4638d9bf07845d@81.7.17.202:9735
eclair
eclair-cli connect 0366217f4a7abf70842f794e94a4cbddc249d5cbaf9c0ffd0b7e4638d9bf07845d@81.7.17.202:9735
(please be note that you have to remove hyphens from the line above, after copy/paste somewhere) or try my already working online tipping tool. Check it out! Send me some Satoshis throught the Lightning ⚡️ Network (beta, but fast as lightning!)


